From Data to Decisions: Enhancing Situational Awareness in Security Operations with Data Analytics
Threat actors have continued to bypass advanced security tooling despite the forecast for enterprises worldwide to spend $212 billion on defensive...
Industry best practices, research, toolkits for the Modern SOC
.png?width=990&height=1048&name=LP%20Featured%20Banner%20(5).png)
 Blog
Blog
Threat actors have continued to bypass advanced security tooling despite the forecast for enterprises worldwide to spend $212 billion on defensive...
 Blog
Blog
Security leaders today aren’t just defending infrastructure. They are protecting business continuity, customer trust, and innovation at scale. The...
 Blog
Blog
April 28 – May 01, 2025 | San Francisco, CA | Moscone Center
Booth #6376 | North Expo.
AI could not get here fast enough. By 2028, humanity's...
 Blog
Blog
Google Cloud Next ‘25 is where innovation in the cloud takes center stage, and Netenrich is set to steal the show. If you’re looking to...
 Blog
Blog
Security teams drowning in alerts and starving for insights? DevOps slowed down by security roadblocks. Cloud environments still feel like the...
 Blog
Blog
The rise of sophisticated attack vectors, such as advanced persistent threats (APTs), ransomware, and zero-day exploits, has completely transformed...
 Blog
Blog
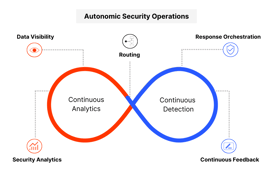
We believe the latest research by Gartner has made one thing clear: the vision of a fully autonomous SOC remains unrealistic. Although automation...
 Blog
Blog
The Chief Information Security Officer (CISO) role has transformed from being purely technical to becoming a strategic business leader. Today's CISOs...
 Blog
Blog
The increasing complexity and scale of cyber threats—fueled by AI and sophisticated tactics—have forced organizations to rethink how they secure...
 Blog
Blog
Security operations (SOC) leaders dream of having a fully scaled unit of security analysts equipped with advanced tools and automation to...
 Blog
Blog
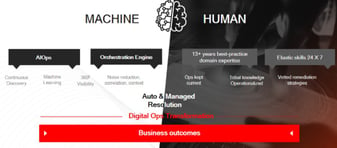
Today adaptable, context-aware SecOps are vital for managing advanced cyber threats. While AI lays the foundation for this SOC adaptability,...
 Blog
Blog
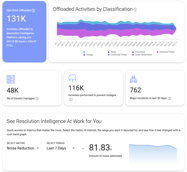
Low signal-to-noise ratios are slowing you down—here’s how to turn noise into clarity.
 Blog
Blog
Traditional SIEMs just aren’t cutting it anymore. They rely on outdated, reactive measures that lead to inefficiencies, false positives, and missed...
 Blog
Blog
Staying informed about emerging technologies is essential in cybersecurity. The Gartner® Hype Cycle™ for Security Operations 2024 report highlights...
 Blog
Blog
Are you ready to take your NFL game day to the next level? Netenrich and Google are teaming up to offer an exclusive opportunity that combines the...
 Blog
Blog
In today's rapidly evolving threat landscape, the need for robust Managed Detection and Response (MDR) solutions has never been greater. Yet,...
 Blog
Blog
Security is a delicate balance of trust and vigilance. To truly automate and innovate, analytics must be more than just powerful. They need to be...
In an industry where we pride ourselves on staying one step ahead of threats, the recent widespread system outages caused by a CrowdStrike update...
 Blog
Blog
As technology evolves at an unprecedented pace and artificial intelligence (AI) becomes an integral part of our daily lives, cybersecurity...
 Blog
Blog
In an era of escalating cyber threats, understanding the evolving landscape of security operations is crucial. Our recent Hybrid SOC and Security...
 Blog
Blog
Remember Ferris Bueller? In a way, working in a SOC is like a high-stakes adventure straight out of Ferris’ playbook. Much like Ferris, who...
The traditional Security Operations Center (SOC) is at a critical juncture. The familiar image of analysts constantly reacting to a relentless...
“In cybersecurity, the only constant is change.” This age-old adage continues to ring true as organizations navigate a shifting threat landscape with...
 Blog
Blog
This is a preliminary report based only on the data leak site (DLS), listed victims, and other observed patterns. A detailed investigation will...
 Blog
Blog
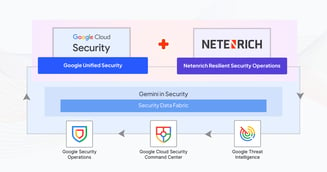
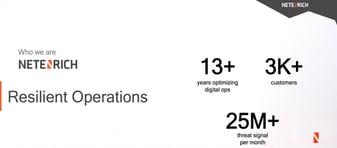
As the first, exclusive pure-play Google SecOps partner, Netenrich is 100% committed to Google SecOps, Mandiant technology stacks as well as our...
 Blog
Blog
This article focuses on my research to uncoverthe identity of Hunters International ransomware group’s (Surface Web) Dedicated Leak Site (DLS). It...
 Blog
Blog
Alpha ransomware, a distinct group not to be confused with ALPHV ransomware, has recently emerged with the launch of its Dedicated/Data Leak Site...
 Blog
Blog
Visit Netenrich at booth #4424 in Moscone North Expo during RSAC in San Francisco on May 6 – 9, 2024, and learn how we are redefining MDR services,...
 Blog
Blog
As rising digital connectivity expands the cyber risk plane in 2024, threat actors continue co-opting innovations to pioneer more virulent extortion...
 Blog
Blog
So, what’s a SOC? Some still believe they need a physical SOC building, where they can see, touch, and manage servers. Others feel it’s necessaryto...
 Blog
Blog
In the ever-evolving landscape of cyber threats, it's not surprising that organizations are expanding their cybersecurity budgets to fortify their...
 Blog
Blog
This article is not an in-depth reverse-engineering analysis of a ransomware variant. Rather, it discusses the methods and different techniques...
 Blog
Blog
Beaconing attacks can be difficult—but not impossible—to detect. The more you know about these stealthy attacks, the better you’ll be able to...
 Blog
Blog
With the rise of generative AI models, the threat landscape has changed drastically. Now, recent activities on the Dark Web Forum show evidence of...
 Blog
Blog
Netenrich has entered into a strategic partnership with Cybriant, a leading managed security services provider (MSSP) that serves more than 1,400...
 Blog
Blog
To keep an enterprise up and running, security is essential—and no doubt, why security teams keep more than busy. Day in, day out, they are...
 Blog
Blog
The internet is a goldmine — but also a jungle — of threat intelligence. You can certainly turn to it to track exploits, vulnerabilities, and...
 Blog
Blog
Detection engineering is the process of designing and implementing systems, tools, and processes — for example, security information and event...
 Blog
Blog
User entity and behavior analytics (UEBA) has been great at solving some significant shortcomings of SIEM (security information and event management)...
 Blog
Blog
According to the Gartner report, “Automated moving target defense (ATMD) technologies are paving the way for a new era of cyber defense...
 Blog
Blog
Netenrich and Google Cloud have joined forces to offer a Fast-Track OEM program for security product innovation. Now security solution providers can...
 Blog
Blog
Wondering what to see and who to visit at RSA 2023? Enterprise Management Associates (EMA) named Netenrich one of the top 10 “must see” vendors at...
 Blog
Blog
Ignore the hype: Artificial intelligence (AI) can improve your security posture now. We’ve been waiting for AI to deliver benefits to cybersecurity...
 Blog
Blog
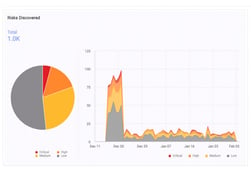
If you’re in security, you probably have some tool somewhere showing a lot of events. Verizon Data Breach Investigation Reports consistently show...
 Blog
Blog
This year, the theme for International Women’s Day is #EmbraceEquity because when you embrace equity, you will, in turn, embrace diversity and...
 Blog
Blog
Heading into 2023 with digital transformation still top of mind for most organizations, CIOs should focus less on what may be new and shiny and more...
 Blog
Blog
Security information and event management (SIEM) and security orchestration, automation, and response (SOAR) are complementary solutions.
 Blog
Blog
Security information and event management (SIEM) is about collecting, detecting, and responding. That is, collecting data into a single pane of glass...
 Blog
Blog
Visit Netenrich at booth #4241 in Moscone South Expo during RSAC in San Francisco on April 24 - 27, 2023. Netenrich will present and demo Resolution...
 Blog
Blog
At Netenrich, part of what we’re doing is looking "left of bang." Bang (!) is geek speak for when we see detonation of malicious content. What...
 Blog
Blog
Threats start with risks. Understanding risks is really just situational awareness. And that awareness leads to faster and better detection. The...
 Blog
Blog
This time of year, people often ask me about highlights from the past year and what to expect in the new year. As I reflect back on major threats and...
 Blog
Blog
"UEBA, it’s just a use case." – Netenrich CISO Chris Morales
He’s not wrong. But I’d take it a step further. User entity and behavior analytics (...
 Blog
Blog
I recently sat down and interviewed Sharat Ganesh, Google Security product marketing leader, and Jonas Kelley, head of Americas MSSP partnerships for...
 Blog
Blog
One vendor uses 5 patterns, the other uses 500 rules. What’s better?
Anyone who has configured a SIEM or UEBA (e.g., QRadar, Splunk, ArcSight,...
 Blog
Blog
MITRE strategy 10 says measure performance to improve performance. It’s important to set a baseline of where resources spend their time and energy —...
 Blog
Blog
As MITRE points out in strategy 9 of its 11 Strategies of a World-class Cybersecurity Operations Center, cross-functional communication is key to a...
 Blog
Blog
Previous strategies in MITRE’s 11 Strategies of a World-class Cybersecurity Operations Center stressed the importance of collecting the right data —...
 Blog
Blog
Strategy 6 of MITRE’s 11 Strategies of a World-class Cybersecurity Operations Center focuses on cyber threat intelligence (CTI) data. Strategy 7, on...
 Blog
Blog
The fifth strategy in MITRE’s 11 Strategies of a World-class Cybersecurity Operations Center counsels organizations to prioritize incident response...
 Blog
Blog
Continuing with our series on ways Resolution Intelligence Cloud helps organizations implement the strategies in MITRE’s 11 Strategies of a...
 Blog
Blog
In our blogs, “Data in Context Is Everything to Security Operations” and “Give SOCs the Authority to Be a Top Business Priority," we began discussing...
 Blog
Blog
In its latest book, 11 Strategies of a World-class Cybersecurity Operations Center, MITRE states that while SOCs perform critical work protecting...
 Blog
Blog
MITRE, a U.S.-based tech foundation for the public good, recently released 11 Strategies of a World-class Cybersecurity Operations Center — an...
 Blog
Blog
Conversation with Chris Morales, Netenrich CISO, originally published on Comptia by Michelle Lange.
Source: Original story published in CompTIA
 Blog
Blog
Security analysts face plethora of alerts while lacking the means and intelligence to quickly investigate, detect, and respond to the most critical...
 Blog
Blog
Source: Originally published in MSSP Alert on Aug 15 2022
 Blog
Keep Reading
Blog
Keep Reading
 Blog
Blog
Resolution Intelligence platform integrated with Google Chronicle is the solution to address the limitations of big data problem.
 Blog
Blog
Digitalization initiatives evolved faster than digital operations in 2020, and 2021 widened the gap even further. But maybe that was a good thing.
 Blog
Blog
Newly available survey results from Dimensional Research confirm the growing need—and appetite—for security operations (SecOps) to become more...
 Blog
Blog
Cyrptocurrency scams are on the rise impacting businesses and workers. Be aware of the latest tactics and learn ways to protect yourself and your...
 Blog
Blog
“Burnout is a real concern, not only for security professionals, but for all IT-related talent. Given that enterprises are asking more...
 Blog
Blog
Troy Abegglen, Customer Success Manager at Netenrich, was the speaker at a recent webinar entitled, ”Reduce 90 Percent Noise Reduction in just 50...
 Blog
Blog
With digital transformation being the goal, learn how to modernize IT operations for improved digital customer experience and IT...
 Blog
Blog
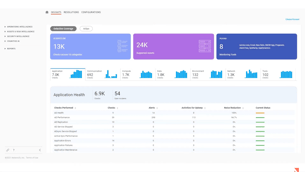
See how our classification and context features power an outcomes-driven IT org for you. Netenrich’s Resolution Intelligence Cloud platform...
 Blog
Blog
Cybersecurity risks often go through the roof when your organization goes through mergers & acquisitions (M&A) and cloud migrations. However, proper...
 Blog
Blog
As Netenrich rolls out our Resolution Intelligence Cloud™ ITOps platform, it seems appropriate to ask what exactly it would mean for enterprises to...
 Blog
Blog
Abhishek Bhuyan, Senior Product Architect at Netenrich, and Matt Bromiley, SANS digital forensics and incident response instructor, recently held a...
 Blog
Blog
Short answer: all the time. Since that doesn’t happen, there are some powerful “inflection points” for taking stock of your digital attack surface...
 Blog
Blog
Brandon Hoffman, Netenrich CISO, was a panelist in the recently completed Information Systems Security Association International (ISSA) webinar...
 Blog
Blog
Every CISO or IT leader has experienced the tough conversations informing the C-Suite and Board of Directors that their company has been breached....
 Blog
Blog
I had the delight in talking with fellow security experts about the Microsoft Exchange attack in a recent webinar. We’re getting many...
 Blog
Blog
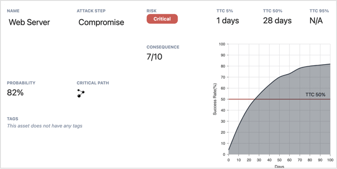
Attack surface management (ASM) and cyber threat intelligence provide protection your organization needs to defend its brands and assets. ASM offers...
 Blog
Blog
How Attack Surface Exposure (ASE) accelerates resolution of digital risks. Pen testing? Pfftt! Try ASE and say goodbye to pen-testing....
 Blog
Blog
Technology has become a vital part of your business endeavors. The year 2020 intensified the demand for IT services. Organizations accelerated...
 Blog
Blog
Netenrich leads efforts to help managed service providers modernize IT services to accelerate business growth.
 Blog
Blog
For most of us, 2020 was a year like no other, defined by the most disruptive and defining event of the past 100 years. As surreal as it felt to have...
 Blog
Blog
“The second you say you’re a SaaS platform, people start asking questions about security,” says Viswanatha Penmetsa, Director of SaaS Operations at
 Blog
Blog
Pulling security activities out of the NOC into dedicated Security Operations Centers (SOCs) sounds like a good thing. Centralize handling of...
 Videos & Webinars
Videos & Webinars
Raju Chekuri, CEO and Chairman of Netenrich, discusses why Netenrich selected Google Cloud Security as its strategic partner to transform enterprise...
 Videos & Webinars
Videos & Webinars
Raju Chekuri, CEO and Chairman of Netenrich, talks about security challenges and the secure operations approach that Netenrich takes with the...
 Videos & Webinars
Videos & Webinars
Netenrich Enterprise Security Architect Michael Perrault discusses how Netenrich has revolutionized its SOC by leveraging our Resolution...
 Videos & Webinars
Videos & Webinars
This video explains how the Netenrich Resolution Intelligence Cloud platform assists businesses in achieving the four-pillar structure of Autonomic...
 Videos & Webinars
Videos & Webinars
This video explains how Resolution Intelligence Cloud helps organizations achieve Autonomic Security Operations (ASO). You will learn the benefits...
 Videos & Webinars
Videos & Webinars
In this video, we demonstrate how to search for data and information of interest within the ActOn interface. An example we present reveals a current...
 Videos & Webinars
Videos & Webinars
This video demonstrates how the Resolution Intelligence Cloud platform connects everything from assets and services to escalation policies, routing,...
 Videos & Webinars
Videos & Webinars
ActOns are linked to services and escalation policies. In this video, we demonstrate:
 Videos & Webinars
Videos & Webinars
This video demonstrates how Resolution Intelligence Cloud™ employs impact-based escalation criteria to automatically distribute ActOns (actionable...
 Videos & Webinars
Videos & Webinars
In this video, we'll demonstrate how an ActOn enables operators to aggregate actionable intelligence in one place — within Resolution Intelligence...
 Videos & Webinars
Videos & Webinars
Netenrich and Cybriant join for a lively discussion on how Cybriant is pushing the envelope in optimizing threat management and response for their...
 Videos & Webinars
Videos & Webinars
Casey John Ellis, co-founder of Bugcrowd and Disclose.io, joins us on this episode of the DEATH Labs podcast to discuss the evolution of bug bounty...
 Videos & Webinars
Videos & Webinars
3,000+ alerts per month and a 95% false positive ratio… Sound familiar? Add the overwhelming complexities of siloed teams and underperforming tools.
 Videos & Webinars
Videos & Webinars
Managing security and digital operations has become far more challenging due to increasing threats and increasing infrastructure complexity.
 Videos & Webinars
Videos & Webinars
Google Cloud security experts Dr. Anton Chuvakin and Timothy Peacock lead a provocative conversation around modern day SIEM in their latest episode....
 Videos & Webinars
Videos & Webinars
In this episode, we are joined by Dr. Anton Chuvakin, Office of the CISO, at Google Cloud Security where we discuss the evolution of SIEM from...
 Videos & Webinars
Videos & Webinars
We are joined this week by John Giglio, director of cloud security for SADA, with tales from the trenches on how automation has helped threat...
 Videos & Webinars
Videos & Webinars
Netenrich’s John Bambenek chats with Merys Raymer, Partner Engineering at Google Cloud Security. Merys shares her personal journey as a former threat...
 Videos & Webinars
Videos & Webinars
John Pirc, VP and Head of Product Management at Netenrich, explains how customers can improve their threat research using Netenrich's Resolution...
 Videos & Webinars
Videos & Webinars
Netenrich's VP and Head of Product Management, John Pirc, discusses how customers can improve their security with data analytics and Resolution...
 Videos & Webinars
Videos & Webinars
John Pirc, VP and Head of Product Management, Netenrich, explains how the Resolution Intelligence Cloud works in a Cybersecurity Mesh Architecture...
 Videos & Webinars
Videos & Webinars
Netenrich's VP and Head of Product Management, John Pirc, outlines the important business and operational outcomes of using the Resolution...
 Videos & Webinars
Videos & Webinars
John Pirc, Netenrich's VP and Head of Product Management, talks about how Resolution Intelligence Cloud works and how it solves the six most critical...
 Videos & Webinars
Videos & Webinars
Netenrich's John Pirc, VP and Head of Product Management, highlights the six major security issues addressed by Resolution Intelligence Cloud. He...
 Videos & Webinars
Videos & Webinars
Raju Chekuri, Chairman and CEO of Netenrich, says that security is causing a significant shift in the ecosystem. This shift will result in the...
 Videos & Webinars
Videos & Webinars
Sharat Ganesh, Head of Product Marketing at Google Chronicle, shares his thoughts on enterprise security concerns. He emphasizes security data for...
 Videos & Webinars
Videos & Webinars
Jonas Kelley, Google Cloud's Head of MSSP Partnerships, shares his thoughts on the importance of context and data in security.
 Videos & Webinars
Videos & Webinars
Jonas Kelley, Head of MSSP Partnerships, Google Cloud, answers John Pirc, VP of Product Marketing at Netenrich, about the top threats organizations...
 Videos & Webinars
Videos & Webinars
The Head of Product Marketing at Google Chronicle, Sharat Ganesh, offers his forecasts for the most important security concerns in the year 2023.
 Videos & Webinars
Videos & Webinars
Sharat Ganesh, Product Marketing Head at Google Chronicle, highlights the significance of bridging the IT-security operations gap. He underlines the...
 Videos & Webinars
Videos & Webinars
Sharat Ganesh, Head of Product Marketing at Google Chronicle, asks John Pirc, VP of Product Marketing at Netenrich, about their partnership with...
 Videos & Webinars
Videos & Webinars
Resolution Intelligence Cloud boosts digital ops productivity with AIOps and automation while giving you comprehensive observability across IT and...
 Videos & Webinars
Videos & Webinars
Join David Swift, Netenrich's Principal Cybersecurity Strategist and Platform Evangelist in this feature walkthrough of Resolution Intelligence...
 Videos & Webinars
Videos & Webinars
Many organizations overlook too many of their digital assets when it comes to managing your security perimeter. Does your perimeter include your...
 Videos & Webinars
Videos & Webinars
Simon Aldama, a Netenrich Advisor, demonstrates Resolution Intelligence's Cyber Situational Awareness modules in this demo.
 Videos & Webinars
Videos & Webinars
Netenrich's Resolution Intelligence streamlines incident management to avoid future disruptions and provides cyber resilience for digital operations.
 Videos & Webinars
Videos & Webinars
Continuing to buy more tools and hire more people does not necessarily lead to better security. While it may improve security postures in the...
 Videos & Webinars
Videos & Webinars
John Bambenek, Principal Threat Hunter, explains how low-detection phishing kits are being utilized to circumvent multifactor authentication (MFA).
 Videos & Webinars
Videos & Webinars
SOC teams are suffering from overwork while threats, infrastructure, data, and business transformation continue to expand. Relief is here. Join this...
 Videos & Webinars
Videos & Webinars
The pandemic rapidly accelerated digital transformation for organizations around the world. Now that the pandemic is behind us, new risks and new...
 Videos & Webinars
Videos & Webinars
John Pirc, VP of Product Management at Netenrich, details the current challenges in defending today’s attack surface and the core tenants of CSMA.
 Videos & Webinars
Videos & Webinars
John Bambenek, Principal Threat Hunter, explains how FontOnLake targets Linux systems and gives attackers remote access to infected devices.
 Videos & Webinars
Videos & Webinars
To deliver competitive digital experiences, enterprises need Resolution Intelligence to monitor top-down, go beyond infrastructure, and make their...
 Videos & Webinars
Videos & Webinars
The current state and challenges of cybersecurity with Chuck Harold of SecurityGuyTV.com.
 Videos & Webinars
Videos & Webinars
Reverse the tide of operational complexity to reduce noise, improve incident response, and increase efficiency exponentially.
 Videos & Webinars
Videos & Webinars
Learn how to identify the right risks and mitigate them quickly in the digital transformation era.
 Videos & Webinars
Videos & Webinars
Raju Chekuri, CEO of Netenrich, and Justin Crotty, SVP of Channels at Netenrich, delve deeper into the 5 key business priorities for MSPs.
Learn about Digital Experience Monitoring and analytics approach to digital operations.
 Videos & Webinars
Videos & Webinars
Maximize end-user customer experience across your users' interactions with your apps and services.
 Videos & Webinars
Videos & Webinars
Learn why it's becoming more important to have security embedded across all secure operations and digital operations.
 Videos & Webinars
Videos & Webinars
Learn how service providers can be more successful and efficient at identifying and resolving problems.
 Videos & Webinars
Videos & Webinars
Justin Crotty, VP of Channels and Simon Aldama, Sr. Director of RiskOps Solutions, talk about Resolution Intelligence Cloud for modern security...
 Videos & Webinars
Videos & Webinars
Take IT Operations to the next level by enabling stability, resilience, and performance.
 Videos & Webinars
Videos & Webinars
Modernize NOC and SOC Ops to reduce IT’s workload while delivering better outcomes.
 Videos & Webinars
Videos & Webinars
Core to business initiatives and delivering outcomes. Solving security problems is now a shared responsibility between DevOps and NetOps teams.
 Videos & Webinars
Videos & Webinars
Rich Lane discusses the significance of data-driven operations and how to better understand your digital operations.
 Videos & Webinars
Videos & Webinars
Bringing in new tools won’t get you where you need to go. It's best to anticipate and prevent outages from occurring.
 Videos & Webinars
Videos & Webinars
Protect assets in the cloud, outsourced critical infrastructure, and other off-prem resources from DDoS.
 Videos & Webinars
Videos & Webinars
Learn how automation can help you correlate information and identify patterns to give analysts a data-rich, complete view of the issue.
 Videos & Webinars
Videos & Webinars
More than 6,000 vCenter installations potentially at risk as RCE exploits surface online.
 Videos & Webinars
Videos & Webinars
Learn how MSPs are innovating services for scale and growth.
 Videos & Webinars
Videos & Webinars
Fine tune your service offerings with a data-driven digital operations (Digital Ops) model
 Videos & Webinars
Keep Reading
Videos & Webinars
Keep Reading
 Videos & Webinars
Videos & Webinars
Join Netenrich experts John Bambenek and Rich Lane to learn how a RiskOps-driven approach orients your digital operations around a proactive new...
 Videos & Webinars
Videos & Webinars
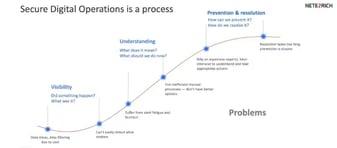
Ops teams buy tools to gain visibility into their environments but still can’t achieve situational awareness while dealing with incidents. It’s time...
 Videos & Webinars
Videos & Webinars
In an industry plagued with buzzwords, “RiskOps” is an idea whose time has come. As transformation accelerates, survival depends on creating true...
 Videos & Webinars
Videos & Webinars
Cybersecurity is war, so why not borrow concepts from U.S. armed forces? Join Netenrich for an introduction to situational awareness as it applies to...
 Videos & Webinars
Videos & Webinars
About ActualTech Media EcoCast Events: The EcoCast is a smaller version of our MegaCast event and provide a variety of both broad and somewhat...
 Videos & Webinars
Videos & Webinars
Chris Morales (Netenrich), Chris Crowley (Montace), and Eric Parizo (Omdia) discuss some of the latest trends in security operations.
 Case studies
Case studies
Cloud Software Group (CSG), a $4.5 billion global software leader, embarked on a transformative security operations modernization journey. Faced with...
 Case studies
Case studies
Facing a crisis of trust after its previous MDR vendor failed to disclose a security breach, this digital media company was determined to overhaul...
 Case studies
Case studies
A prominent regional bank with over 80 branches across Southern California, headquartered in Los Angeles and backed by more than 2,000 employees...
 Case studies
Case studies
A major healthcare technology company, with over $800M in revenue had relied on Splunk for security operations. However, the complexity, high costs,...
 Case studies
Case studies
Resolution Intelligence Cloud™ operationalizes security at service-provider scale. It’s a cloud native, modern SaaS platform designed for ease of...
 Case studies
Case studies
Netenrich's Resolution Intelligence Cloud's contextualized data enables a large global manufacturer to increase security.
 Case studies
Case studies
Discover how Netenrich's Resolution Intelligence Cloud helps MultiCare with its digital transformation challenges.
 Case studies
Case studies
Read how Resolution Intelligence Cloud™ transformed SysTools, a cybersecurity services provider.
 Case studies
Case studies
Netenrich helps a service provider build scalable, agile enterprise service model to improve their NOC (network operations center).
 Data Sheets
Data Sheets
Migrating to Google Security Operations platform is a game changer for your organization’s...
 Data Sheets
Data Sheets
Netenrich SecOps Operate provides continuous, expert-led engineering to ensure Google SecOps is...
 Data Sheets
Data Sheets
Because a One-Size-Fits-All MDR ... Fits No One!
Not all businesses operate the same way, which is why a one-size-fits-all or standardized MDR has...
 Data Sheets
Data Sheets
Resolution Intelligence Cloud is a cloud-native data analytics platform for managing risk and optimizing overall operations, with the scale and speed...
 Data Sheets
Data Sheets
Resolution Intelligence Cloud™ is a cloud-native data analytics platform for managing security and digital operations, with the scale and speed of...
 Data Sheets
Data Sheets
Resolution Intelligence Cloud is a cloud-native platform for managing digital operations efficiently and effectively at scale with operational data...
 Data Sheets
Data Sheets
Attack Surface Exposure (ASE) combines security expertise and artificial intelligence (AI) to deliver complete Resolution Intelligence.
 Data Sheets
Data Sheets
Monitoring is important. Detection is important. Resolution is critical. You’ve... |
 Guides
Guides
Google Chronicle, part of Google SecOps, is a powerful tool for security data analysis at organizations regardless of size. Using the platform...
 Guides
Guides
Netenrich's Adaptive MDR™ solution is designed to enable proactive and continuous detection and response that helps minimize the impact of security...
 Guides
Guides
What exactly is Autonomic Security Operations (ASO), and why do many of the best minds in cybersecurity think it’s the future of security...
 Guides
Guides
Implement MITRE’s recommended world-class SOC strategies using the Netenrich Resolution Intelligence Cloud platform.
 Guides
Guides
Implement an open mesh architecture for cybersecurity — and all digital operations.
 Guides
Guides
Secure operations — different from security operations and security operations centers (SOCs) — is a new approach to security and digital...
 Guides
Guides
This guide explains seven times to attack your attack surface, what you should investigate and, shore up your attack surface.
 Guides
Guides
This guide helps CISOs, CIOs, and their boards to manage cybersecurity risk and, in the process, reduce exposure to harm.
 Guides
Guides
This is an MSSP Technology Checklist of threat detection and security operations challenges facing MSSPs and what should look for now and next.
 Guides
Guides
This guide helps CISOs, CIOs, and their boards to manage cybersecurity risk and, in the process, reduce exposure to harm.
 Guides
Guides
Right-size tool strategies, bridge skills gaps, and align operations with your goals for the business.
 Guides
Guides
The attack surface is the sum of all internet-facing digital assets, hardware, software, and applications that can be exploited to carry out...
 Guides
Guides
Security tests serve different needs and have different methodologies. In this article, we go over the differences between attack surface...
 Guides
Guides
People often get the terms attack surface, and attack vector confused. Though these terms are related, they hold a different meaning altogether.
 Reports
Reports
Netenrich commissioned a third-party organization to conduct a security survey across U.S-based organizations with more than 500 employees.
 Reports
Reports
Matt Bromiley, a SANS Certified Instructor, reviews Netenrich's Resolution Intelligence Cloud™, a SaaS platform that integrates XDR, SOAR, and SIEM.
 Reports
Reports
The latest survey results from Dimensional Research highlight the growing need for risk-driven security operations (SecOps).
 Reports
Reports
This research reviews key findings from a global survey on how companies manage their attack surface.
 Reports
Reports
Read what SANS says about Netenrich's Attack Surface Intelligence (ASI)* and how it provides industry-leading insights.
*Please note, Attack Surface...
 Reports
Reports
Netenrich teamed up with EMA to outline the steps for implementing situational awareness for proactive, risk-aligned security.