Autonomous Security Operations - AI Driven Automation for Resilient SecOps
Unleash your SOC's True Potential: From Toil to Strategic Oversight
Free your security experts from the noise of repetitive alerts. Netenrich Autonomous Security Operations applies Agentic AI that acts on your behalf, autonomously handling known threats and repetitive tasks. This AI Core ruthlessly automates the known and adapts playbooks in real time, while your analysts shift from alert-chasing to strategic oversight.
.png?width=900&height=900&name=Autonomous%20SOC%20(1).png)
World’s Best Data-driven Security Teams Count on us







_2013-11-24_16-00.png?width=1024&height=293&name=1024px-Tibco_logo-_Palo_Alto%2c_CA_company-_(PNG)_2013-11-24_16-00.png)

“We didn’t need more playbooks, we needed adaptive response flows that fit our environment.
Netenrich brought the context and automation that transformed how we respond.”
— CISO, Global Enterprise
Your Security Operations are at a Tipping Point
Even the best SOC models degrade within 3-4 years, buried in toil, tool fatigue, and alert noise. Old playbooks are reactive and static, while attackers move in minutes, not days.
.png?width=30&height=30&name=tick%20(2).png) Limited Visibility from Fragmented Tools
Limited Visibility from Fragmented Tools
Fragmented tools and manual processes block real-time insights across cloud, on-prem, and remote endpoints thereby leaving blind spots..png?width=30&height=30&name=tick%20(2).png) Alert Overload and Constant Firefighting
Alert Overload and Constant Firefighting
Analysts drown in endless alerts and reactive workflows, chasing noise instead of anticipating the next threat..png?width=30&height=30&name=tick%20(2).png) Growing Talent Drain
Growing Talent Drain
Skilled experts burn out, reduced to tool operators instead of true threat hunters.
Free Up Intellect. Focus on What Matters.
Netenrich Autonomous Security Operations replaces reactive models with proactive, automation-first SecOps. By embedding Agentic AI into detection, triage, and response, CISOs achieve resilience without scaling headcount.
Automate the Known with an AI Core
We build an AI Core that ruthlessly automates repetitive triage, enrichment, and ticket handling. This eliminates noise and accelerates response time.

Shift from Reactive to Proactive Investigations
With noise eliminated, analysts transform into AI Supervisors and proactive threat hunters. Instead of chasing tickets, they run hypothesis-driven investigations, validate anomalies, and assess business risk across APIs, containers, identities, and AI-driven services.

.png?width=25&height=25&name=tick%20(2).png) Always-On Defense
Always-On Defense
.png?width=25&height=25&name=tick%20(2).png) Noise-Free Operations
Noise-Free Operations
.png?width=25&height=25&name=tick%20(2).png) Faster Incident Response
Faster Incident Response
.png?width=25&height=25&name=tick%20(2).png) Resilient SecOps at Scale
Resilient SecOps at Scale
Modernize your Security Operations with Netenrich
Unlike tool-heavy SOC models, Netenrich combines AI-driven SecOps automation with deep security expertise to deliver:

52%+ lower operating costs

Faster MTTD/MTTR with automated workflows

Integrated MDR services for ongoing resilience

Proactive visibility into known and unknown threats
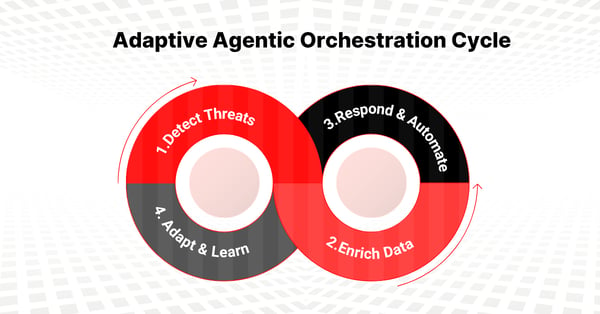
Adaptive Agentic Orchestration
Our specialized AI agents orchestrate detection, enrichment, and response across your stack, transforming static SOAR playbooks into adaptive, context-aware automation.

From Alert Operators to AI Supervisors.
Analysts aren’t replaced, they’re elevated. As AI Supervisors, they focus on ensuring the system works as expected: validating AI outputs, spotting gaps, and strengthening detections. Instead of just reviewing alerts, they guide efficacy and outcomes.
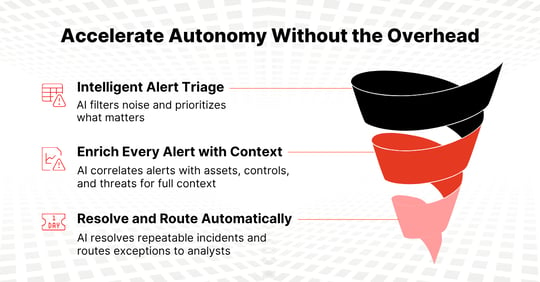
Accelerate Autonomy Without the Overhead
Building and maintaining an autonomous SOC on your own takes years of engineering and scarce AI/ML expertise. With Netenrich, you get the outcomes without the burden. We embed our experts, co-source capabilities, and continuously evolve your SOC into a semi-autonomous model that delivers results fast.
Frequently Asked Questions (FAQs)
-
1. What is an AI SOC and why does it matter for CISOs?
An AI SOC uses autonomous SOC automation to cut false positives, reduce analyst toil, and accelerate response, giving CISOs stronger visibility, control, and operational efficiency.
-
2. What’s the difference between Agentic AI SecOps and Autonomous Security Operations?
Agentic AI involves intelligent agents that reason, adapt, and coordinate across workflows; essentially the tooling, from a SecOps perspective. Autonomous Security Operations is the outcome: resilient, always-on security where AI handles the noise and analysts focus on what matters.
-
3. How does Netenrich AI-driven SOC automation improve security operations?
Netenrich’s AI-driven SOC automation eliminates alert fatigue by automating known threats, repetitive tasks, and triage.
-
4. Does Autonomous SOC replace my security team?
No. Autonomous SOC augments your SOC analysts by automating repetitive tasks so they can focus on strategic investigations and risk management.
-
5. How quickly can a CISO see value from Netenrich ?
Most organizations see measurable efficiency gains within weeks. Netenrich delivers rapid onboarding, automation of high-volume tasks, and early reduction in alert fatigue.
Work from a common operational view
Siloed security and digital ops leads to gaps and inefficient duplication of tools, processes, and people. Resolution Intelligence Cloud provides a common operational view and situational awareness aligned to business risk. And it facilitates collaboration within and between teams.
- Strengthen your security posture
- Improve performance and up time
- Boost analyst effectiveness
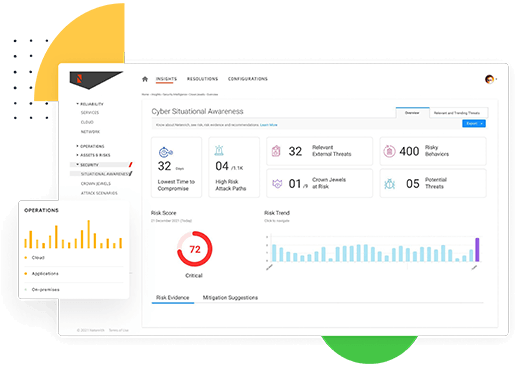
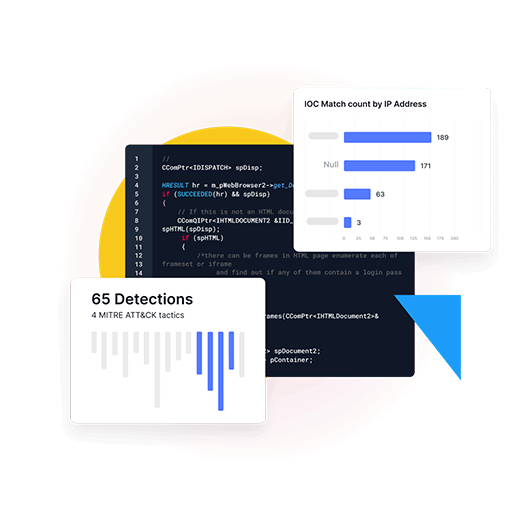
Out-innovate hackers with anomaly detection & situational awareness
Hackers are relentlessly innovative. It's futile to fight them with traditional, reactive methods.
- Identify unknowns without detection rules with advanced anomaly detection (think next-next-gen UEBA)
- Be proactive with actionable insights from data over time, correlated and mapped to the MITRE ATT&CK framework
- Identify and resolve what matters most to the business — stop wasting time on alert noise
- Communicate across functions and coordinate response fast
Ready to Redefine Your Team's Mission?
Let’s map a practical path to a semi-autonomous Security Operations with AI supervision. Schedule a strategy session and start ruthlessly automating the known, so your team can focus on the unknown.

