GenAI: Building a Foundation for AI in Cybersecurity
When I talk about Netenrich's use of large language models and agentic systems, I sometimes get a specific question: how did you move so quickly?
Solutions
Why Netenrich
Company
Partner Programs
Technology Partners
Key Resources
 Blog
Blog
When I talk about Netenrich's use of large language models and agentic systems, I sometimes get a specific question: how did you move so quickly?
 Blog
Blog
Modern cloud environments have fundamentally changed how enterprise data is stored, accessed, and operationalized. Platforms like Google BigQuery now...
 Blog
Blog
Non-Human Identities (NHIs)—service accounts, automation tokens, CI/CD pipeline credentials, and cloud IAM roles—now outnumber human users in most...
As modern enterprises scale, their security operations inevitably face a daunting challenge: managing the explosive volume of telemetry data. For...
.png?width=337&height=172&name=25%20weeks%20blogs%20banners%20(18).png) Blog
Blog
When we started building the Resolution Intelligence Cloud in 2018, one of the first major investments we made was in something that would never...
.png?width=337&height=172&name=25%20weeks%20blogs%20banners%20(17).png) Blog
Blog
When I committed to making Netenrich a data-first, intelligence-first security company in 2018, I did something that made some people question my...
.png?width=337&height=172&name=25%20weeks%20blogs%20banners%20(15).png) Blog
Blog
There is a pattern in how security programs try to improve detection quality that I have observed consistently, and that consistently produces...
 Blog
Blog
How Netenrich and Google AI Threat Defense close the loop between finding vulnerabilities and surviving exploitation
 Blog
Blog
AI promises to transform the Security Operations Center and in many cases, it does. But a dangerous gap exists between the appearance of efficiency...
.png?width=337&height=172&name=25%20weeks%20blogs%20banners%20(14).png) Blog
Blog
I want to tell you a story I don't talk about often enough. Not because it is painful, it no longer is. But because the lessons in it are the ones...
 Blog
Blog
By Christopher Morales, CISO and Head of Security Strategy, Netenrich
I’ve spent enough time in this industry to see a lot of "innovative" approaches...
 Blog
Blog
The configuration management database is one of those enterprise systems that almost everyone has and almost no one fully trusts. I say this not as a...
 Blog
Blog
Most security frameworks describe the enterprise as a collection of assets: servers, endpoints, cloud instances, applications, users. You protect the...
 Blog
Blog
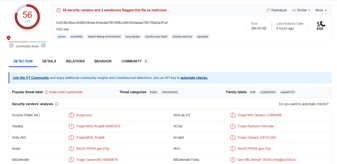
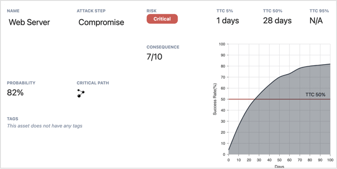
Security teams face a persistent vulnerability prioritization problem. At any given moment, there are more alerts, more vulnerabilities, more threat...
 Blog
Blog
Most security frameworks describe the enterprise as a collection of assets: servers, endpoints, cloud instances, applications, users. You protect the...
 Blog
Blog
I’ve been in this game for over two decades, and if there’s one thing that hasn’t changed, it’s our industry's obsession with throwing bodies and...
 Blog
Blog
Ask any CISO in any organization of any size: do you know your complete attack surface right now?
 Blog
Blog
In 2018, I had just watched OpsRamp find its home at HPE. Six years of building a genuinely cloud-native IT operations platform - designed from the...
 Blog
Blog
On March 24, 2026, two malicious versions of the litellm Python package - v1.82.7 and v1.82.8 - were published to PyPI as part of a broader...
 Blog
Blog
From the CEO’s Desk
Raju Chekuri, Chairman, President & CEO of Netenrich, shares a candid perspective shaped by conversations with CISOs and CIOs...
 Blog
Blog
A CISO's Mandate: Stop Traditional Outsourcing, Start Transforming
The Financial Sector Cannot Afford Yesterday's Security Model
The world has...
 Blog
Blog
Cyberattacks rarely begin with masterful exploits. They start with small lapses, a forgotten firewall rule, a disabled endpoint agent, an exposed...
 Blog
Blog
On a regular Monday morning, Maya, an SOC lead, logs into her company’s asset inventory. Instead of clarity, she is greeted by something very...
 Blog
Blog
Security Operations Centers (SOCs) are busier than ever. However, are they more effective? Alerts pile up, queues grow, and teams work nonstop just...
 Blog
Blog
The modern Security Operations Center (SOC) is drowning in noise. Each new security tool, from SIEMs to EDRs, brings its own stream of alerts, rules,...
 Blog
Blog
Most security teams don’t suffer from a lack of tools; they suffer from too many. Years of adding products to cover new threats have left many SOCs...
 Blog
Blog
Attackers move faster than defenders can blink. In 2024, the average breakout time for an attack dropped to 48 minutes, with some intrusions...
 Blog
Blog
In today's digital landscape, seeing the full risk picture is no longer an advantage – it's a requirement for survival. Most enterprise security...
 Blog
Blog
Artificial intelligence (AI) is no longer optional. It has become a necessity in almost every corporate environment. From product development and...
 Blog
Blog
Securing IT infrastructure is never simple, and hybrid cloud environments raise the stakes further. It’s like managing a single-family home alongside...
 Blog
Blog
CISOs face a paradox. Despite multi-million-dollar investments, the average data breach still costs over $4.4M. The problem isn’t the tools; they...
 Blog
Blog
For more than 15 years, cybersecurity has made use of artificial intelligence (AI) and machine learning,...
 Blog
Blog
Strapline: A security data lake is not a dumping ground - it’s a living, query-ready foundation for precision threat detection, AI-driven insights,...
 Blog
Blog
For today’s cloud-native enterprises, “security by default” is a dangerously misleading concept. Many digital-native organizations, whose entire...
 Blog
Blog
Cyber threats are everywhere. Not only that, they come from everywhere. So while we may win battles, it feels as though we are losing the war....
 Blog
Blog
Incident response methodology is the structured process organizations use to prepare for, detect, contain, and...
 Blog
Blog
API Security is the practice of protecting the application programming interfaces (APIs) that power cloud-first enterprises
 Blog
Blog
Security Operations Centers (SOCs) were designed for yesterday’s threats. In 2025, leaders face new realities:
 Blog
Blog
 Blog
Blog
 Blog
Blog
 Blog
Blog
 Blog
Blog
 Blog
Blog
 Blog
Blog
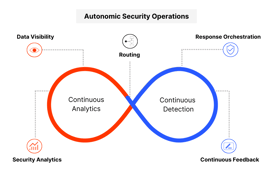
Most security operations centers struggle with scale, complexity, and context. Teams are flooded with alerts from disconnected tools, each focused on...
 Blog
Blog
Cybersecurity in 2025 faces an unprecedented wave of AI-augmented threat actors. Attackers leverage...
 Blog
Blog
Google Chronicle, part of Google SecOps, is a powerful tool for security data analysis at organizations regardless of size. Using the platform...
 Blog
Blog
Threat actors have continued to bypass advanced security tooling despite the forecast for enterprises worldwide to spend $212 billion on defensive...
 Blog
Blog
Security leaders today aren’t just defending infrastructure. They are protecting business continuity, customer trust, and innovation at scale. The...
 Blog
Blog
The rise of sophisticated attack vectors, such as advanced persistent threats (APTs), ransomware, and zero-day exploits, has completely transformed...
 Blog
Blog
The Chief Information Security Officer (CISO) role has transformed from being purely technical to becoming a strategic business leader. Today's CISOs...
 Blog
Blog
The increasing complexity and scale of cyber threats—fueled by AI and sophisticated tactics—have forced organizations to rethink how they secure...
 Blog
Blog
Security operations (SOC) leaders dream of having a fully scaled unit of security analysts equipped with advanced tools and automation to...
 Blog
Blog
Today adaptable, context-aware SecOps are vital for managing advanced cyber threats. While AI lays the foundation for this SOC adaptability,...
 Blog
Blog
Low signal-to-noise ratios are slowing you down—here’s how to turn noise into clarity.
 Blog
Blog
Traditional SIEMs just aren’t cutting it anymore. They rely on outdated, reactive measures that lead to inefficiencies, false positives, and missed...
 Blog
Blog
Are you ready to take your NFL game day to the next level? Netenrich and Google are teaming up to offer an exclusive opportunity that combines the...
 Blog
Blog
In today's rapidly evolving threat landscape, the need for robust Managed Detection and Response (MDR) solutions has never been greater. Yet,...
 Blog
Blog
Security is a delicate balance of trust and vigilance. To truly automate and innovate, analytics must be more than just powerful. They need to be...
 Blog
Blog
As technology evolves at an unprecedented pace and artificial intelligence (AI) becomes an integral part of our daily lives, cybersecurity...
 Blog
Blog
In an era of escalating cyber threats, understanding the evolving landscape of security operations is crucial. Our recent Hybrid SOC and Security...
 Blog
Blog
Remember Ferris Bueller? In a way, working in a SOC is like a high-stakes adventure straight out of Ferris’ playbook. Much like Ferris, who...
The traditional Security Operations Center (SOC) is at a critical juncture. The familiar image of analysts constantly reacting to a relentless...
“In cybersecurity, the only constant is change.” This age-old adage continues to ring true as organizations navigate a shifting threat landscape with...
 Blog
Blog
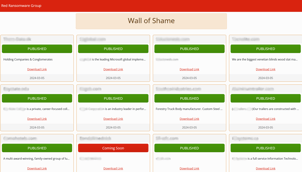
This is a preliminary report based only on the data leak site (DLS), listed victims, and other observed patterns. A detailed investigation will...
 Blog
Blog
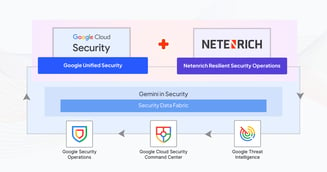
As the first, exclusive pure-play Google SecOps partner, Netenrich is 100% committed to Google SecOps, Mandiant technology stacks as well as our...
 Blog
Blog
This article focuses on my research to uncoverthe identity of Hunters International ransomware group’s (Surface Web) Dedicated Leak Site (DLS). It...
 Blog
Blog
Alpha ransomware, a distinct group not to be confused with ALPHV ransomware, has recently emerged with the launch of its Dedicated/Data Leak Site...
 Blog
Blog
So, what’s a SOC? Some still believe they need a physical SOC building, where they can see, touch, and manage servers. Others feel it’s necessaryto...
 Blog
Blog
This article is not an in-depth reverse-engineering analysis of a ransomware variant. Rather, it discusses the methods and different techniques...
Beaconing attacks can be difficult—but not impossible—to detect. The more you know about these stealthy attacks, the better you’ll be able to...
With the rise of generative AI models, the threat landscape has changed drastically. Now, recent activities on the Dark Web Forum show evidence of...
 Blog
Blog
Netenrich has entered into a strategic partnership with Cybriant, a leading managed security services provider (MSSP) that serves more than 1,400...
 Blog
Blog
To keep an enterprise up and running, security is essential—and no doubt, why security teams keep more than busy. Day in, day out, they are...
 Blog
Blog
Detection engineering is the process of designing and implementing systems, tools, and processes — for example, security information and event...
 Blog
Blog
User entity and behavior analytics (UEBA) has been great at solving some significant shortcomings of SIEM (security information and event management)...
 Blog
Blog
According to the Gartner report, “Automated moving target defense (ATMD) technologies are paving the way for a new era of cyber defense...
 Blog
Blog
Wondering what to see and who to visit at RSA 2023? Enterprise Management Associates (EMA) named Netenrich one of the top 10 “must see” vendors at...
 Blog
Blog
Heading into 2023 with digital transformation still top of mind for most organizations, CIOs should focus less on what may be new and shiny and more...
 Blog
Blog
Security information and event management (SIEM) and security orchestration, automation, and response (SOAR) are complementary solutions.
 Blog
Blog
Security information and event management (SIEM) is about collecting, detecting, and responding. That is, collecting data into a single pane of glass...
 Blog
Blog
"UEBA, it’s just a use case." – Netenrich CISO Chris Morales
He’s not wrong. But I’d take it a step further. User entity and behavior analytics (...
 Blog
Blog
One vendor uses 5 patterns, the other uses 500 rules. What’s better?
Anyone who has configured a SIEM or UEBA (e.g., QRadar, Splunk, ArcSight,...
 Blog
Blog
MITRE strategy 10 says measure performance to improve performance. It’s important to set a baseline of where resources spend their time and energy —...
 Blog
Blog
As MITRE points out in strategy 9 of its 11 Strategies of a World-class Cybersecurity Operations Center, cross-functional communication is key to a...
 Blog
Blog
Digitalization initiatives evolved faster than digital operations in 2020, and 2021 widened the gap even further. But maybe that was a good thing.
 Videos & Webinars
Videos & Webinars
Raju Chekuri, CEO and Chairman of Netenrich, talks about security challenges and the secure operations approach that Netenrich takes with the...
 Case studies
Case studies
As digital transformation increases in the financial sector, security leaders face challenges
 Case studies
Case studies
Cloud Software Group (CSG), a $4.5 billion global software leader, embarked on a transformative security operations modernization journey. Faced with...
 Case studies
Case studies
Facing a crisis of trust after its MDR vendor failed to disclose a security breach, this digital media company was determined to overhaul its...
 Case studies
Case studies
A prominent regional bank with over 80 branches across Southern California, headquartered in Los Angeles and backed by more than 2,000 employees...
 Case studies
Case studies
A major healthcare technology company, with over $800M in revenue had relied on Splunk for security operations. Over time, complexity increased,...
 Case studies
Case studies
Resolution Intelligence Cloud™ operationalizes security at service-provider scale. It’s a cloud native, modern SaaS platform designed for ease of...
 Case studies
Case studies
Discover how Netenrich's Resolution Intelligence Cloud helps MultiCare with its digital transformation challenges.
 Case studies
Case studies
Read how Resolution Intelligence Cloud™ transformed SysTools, a cybersecurity services provider.
 Data Sheets
Data Sheets
Because a One-Size-Fits-All MDR ... Fits No One!
Not all businesses operate the same way, which is why a one-size-fits-all or standardized MDR has...
 Data Sheets
Data Sheets
Resolution Intelligence Cloud is a cloud-native data analytics platform for managing risk and optimizing overall operations, with the scale and speed...
















The best source of information for Security, Networks, Cloud, and ITOps best practices. Join us.