2 min read
Beyond CMDBs: Modernizing IT Asset Management (ITAM)
The configuration management database is one of those enterprise systems that...
Partner Programs
Technology Partners
Key Resources
 Blog
Blog
2 min read
The configuration management database is one of those enterprise systems that...
 Blog
Blog
2 min read
Most security frameworks describe the enterprise as a collection of assets:...
 Blog
Blog
2 min read
Security teams face a persistent vulnerability prioritization problem. At any...
 Blog
Blog
2 min read
Most security frameworks describe the enterprise as a collection of assets:...
 Blog
Blog
4 min read
I’ve been in this game for over two decades, and if there’s one thing that...
 Blog
Blog
2 min read
Ask any CISO in any organization of any size: do you know your complete attack...
 Blog
Blog
2 min read
In 2018, I had just watched OpsRamp find its home at HPE. Six years of building...
 Blog
Blog
13 min read
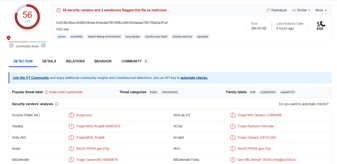
On March 24, 2026, two malicious versions of the litellm Python...
 Blog
Blog
3 min read
From the CEO’s Desk
Raju Chekuri, Chairman, President & CEO of Netenrich,...
 Blog
Blog
3 min read
A CISO's Mandate: Stop Traditional Outsourcing, Start Transforming
The...
 Blog
Blog
7 min read
Cyberattacks rarely begin with masterful exploits. They start with small...
 Blog
Blog
5 min read
On a regular Monday morning, Maya, an SOC lead, logs into her company’s asset...
 Blog
Blog
5 min read
Security Operations Centers (SOCs) are busier than ever. However, are they more...
 Blog
Blog
6 min read
The modern Security Operations Center (SOC) is drowning in noise. Each new...
 Blog
Blog
5 min read
Most security teams don’t suffer from a lack of tools; they suffer from too...
 Blog
Blog
5 min read
Attackers move faster than defenders can blink. In 2024, the average breakout...
 Blog
Blog
6 min read
In today's digital landscape, seeing the full risk picture is no longer an...
 Blog
Blog
6 min read
Artificial intelligence (AI) is no longer optional. It has become a necessity...
 Blog
Blog
5 min read
Securing IT infrastructure is never simple, and hybrid cloud environments raise...
 Blog
Blog
6 min read
CISOs face a paradox. Despite multi-million-dollar investments, the average...
 Blog
Blog
2 min read
For more than 15 years,...
 Blog
Blog
4 min read
Strapline: A security data lake is not a dumping ground - it’s a living,...
 Blog
Blog
4 min read
For today’s cloud-native enterprises, “security by default” is a dangerously...
 Blog
Blog
2 min read
Cyber threats are everywhere. Not only that, they come from everywhere. So...
 Blog
Blog
5 min read
Incident response methodology is the...
 Blog
Blog
5 min read
API Security is the practice of protecting the...
 Blog
Blog
4 min read
Security Operations Centers (SOCs) were designed...
 Blog
Blog
5 min read
 Blog
Blog
5 min read
 Blog
Blog
6 min read
 Blog
Blog
4 min read
 Blog
Blog
5 min read
 Blog
Blog
8 min read
 Blog
Blog
2 min read
Most security operations centers struggle with scale, complexity, and context....
 Blog
Blog
4 min read
Cybersecurity in 2025 faces an...
 Blog
Blog
3 min read
Google Chronicle, part of Google SecOps, is a powerful tool for security data...
 Blog
Blog
6 min read
Threat actors have continued to bypass advanced security tooling despite the...
 Blog
Blog
3 min read
Security leaders today aren’t just defending infrastructure. They are...
 Blog
Blog
5 min read
The rise of sophisticated attack vectors, such as advanced persistent threats...
 Blog
Blog
6 min read
The Chief Information Security Officer (CISO) role has transformed from being...
 Blog
Blog
4 min read
The increasing complexity and scale of cyber threats—fueled by AI and...
 Blog
Blog
5 min read
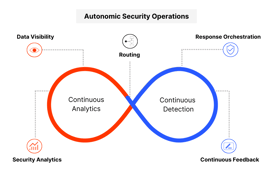
Security operations (SOC) leaders dream of having a fully scaled unit of...
 Blog
Blog
5 min read
Today adaptable, context-aware SecOps are vital for managing advanced cyber...
 Blog
Blog
4 min read
Low signal-to-noise ratios are slowing you down—here’s how to turn noise into...
 Blog
Blog
3 min read
Traditional SIEMs just aren’t cutting it anymore. They rely on outdated,...
 Blog
Blog
1 min read
Are you ready to take your NFL game day to the next level? Netenrich and...
 Blog
Blog
3 min read
In today's rapidly evolving threat landscape, the need for robust Managed...
 Blog
Blog
3 min read
Security is a delicate balance of trust and vigilance. To truly automate and...
 Blog
Blog
2 min read
As technology evolves at an unprecedented pace and artificial intelligence...
 Blog
Blog
2 min read
In an era of escalating cyber threats, understanding the evolving landscape...
 Blog
Blog
3 min read
Remember Ferris Bueller? In a way, working in a SOC is like a high-stakes...
3 min read
The traditional Security Operations Center (SOC) is at a critical juncture....
2 min read
“In cybersecurity, the only constant is change.” This age-old adage continues...
 Blog
Blog
4 min read
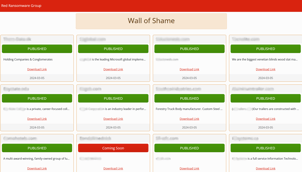
This is a preliminary report based only on the data leak site (DLS), listed...
 Blog
Blog
1 min read
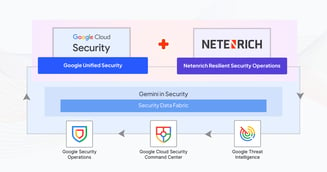
As the first, exclusive pure-play Google SecOps partner, Netenrich is 100%...
 Blog
Blog
5 min read
This article focuses on my research to uncoverthe identity of Hunters...
 Blog
Blog
4 min read
Alpha ransomware, a distinct group not to be confused with ALPHV ransomware,...
 Blog
Blog
4 min read
So, what’s a SOC? Some still believe they need a physical SOC building, where...
 Blog
Blog
8 min read
This article is not an in-depth reverse-engineering analysis of a ransomware...
3 min read
Beaconing attacks can be difficult—but not impossible—to detect. The more you...
2 min read
With the rise of generative AI models, the threat landscape has changed...
 Blog
Blog
1 min read
Netenrich has entered into a strategic partnership with Cybriant, a leading ...
 Blog
Blog
3 min read
To keep an enterprise up and running, security is essential—and no doubt, why...
 Blog
Blog
2 min read
Detection engineering is the process of designing and implementing systems,...
 Blog
Blog
3 min read
User entity and behavior analytics (UEBA) has been great at solving some...
 Blog
Blog
4 min read
According to the Gartner report, “Automated moving target defense (ATMD)...
 Blog
Blog
1 min read
Wondering what to see and who to visit at RSA 2023? Enterprise Management...
 Blog
Blog
4 min read
Heading into 2023 with digital transformation still top of mind for most...
 Blog
Blog
3 min read
Security information and event management (SIEM) and security orchestration,...
 Blog
Blog
4 min read
Security information and event management (SIEM) is about collecting,...
 Blog
Blog
3 min read
"UEBA, it’s just a use case." – Netenrich CISO Chris Morales
He’s not wrong....
 Blog
Blog
4 min read
One vendor uses 5 patterns, the other uses 500 rules. What’s better?
Anyone...
 Blog
Blog
2 min read
MITRE strategy 10 says measure performance to improve performance. It’s...
 Blog
Blog
3 min read
As MITRE points out in strategy 9 of its 11 Strategies of a World-class...
 Blog
Blog
4 min read
Digitalization initiatives evolved faster than digital operations in 2020, and...
 Videos & Webinars
Videos & Webinars
1 min read
Raju Chekuri, CEO and Chairman of Netenrich, talks about security challenges...
 Case studies
Case studies
4 min read
As digital transformation increases in...
 Case studies
Case studies
4 min read
Cloud Software Group (CSG), a $4.5 billion global software leader, embarked on...
 Case studies
Case studies
4 min read
Facing a crisis of trust after its MDR vendor failed to disclose a security...
 Case studies
Case studies
2 min read
A prominent regional bank with over 80 branches across Southern California,...
 Case studies
Case studies
2 min read
A major healthcare technology company, with over $800M in revenue had relied on...
 Case studies
Case studies
3 min read
Resolution Intelligence Cloud™ operationalizes security at service-provider...
 Case studies
Case studies
3 min read
Discover how Netenrich's Resolution Intelligence Cloud helps MultiCare with its...
 Case studies
Case studies
2 min read
Read how Resolution Intelligence Cloud™ transformed SysTools, a cybersecurity...
 Data Sheets
Data Sheets
4 min read
Because a One-Size-Fits-All MDR ... Fits No One!
Not all businesses operate the...
 Data Sheets
Data Sheets
2 min read
Resolution Intelligence Cloud is a cloud-native data analytics platform for...
3 min read
May 21, 2026 by Raju Chekuri
The configuration management database is one of those enterprise systems that...
3 min read
May 19, 2026 by Raju Chekuri
Most security frameworks describe the enterprise as a collection of assets:...
3 min read
May 14, 2026 by Raju Chekuri
Security teams face a persistent vulnerability prioritization problem. At any...
2 min read
Jul 25, 2025 by Michael Beavers
Most security operations centers struggle with scale, complexity, and context....
1 min read
Jul 20, 2023 by Netenrich
Netenrich has entered into a strategic partnership with Cybriant, a leading ...
4 min read
Jul 18, 2023 by John Pirc
To keep an enterprise up and running, security is essential—and no doubt, why...
4 min read
Jun 30, 2025 by Netenrich
Google Chronicle, part of Google SecOps, is a powerful tool for security data...
8 min read
Feb 20, 2025 by Netenrich
The Chief Information Security Officer (CISO) role has transformed from being...
4 min read
Sep 17, 2024 by Raju Chekuri
Traditional SIEMs just aren’t cutting it anymore. They rely on outdated,...
9 min read
Nov 12, 2025 by Netenrich
Cyberattacks rarely begin with masterful exploits. They start with small...
8 min read
Nov 11, 2025 by Netenrich
On a regular Monday morning, Maya, an SOC lead, logs into her company’s asset...
7 min read
Nov 11, 2025 by Netenrich
Security Operations Centers (SOCs) are busier than ever. However, are they more...
















The best source of information for Security, Networks, Cloud, and ITOps best practices. Join us.
