Using Intelligent Data as a Force Multiplier for Security and IT Ops
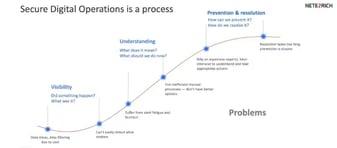
Managing security and digital operations has become far more challenging due to increasing threats and increasing infrastructure complexity.
Watch nowManaging security and digital operations has become far more challenging due to increasing threats and increasing infrastructure complexity.
Watch now
Google Cloud security experts Dr. Anton Chuvakin and Timothy Peacock lead a provocative conversation around modern day SIEM in their latest episode....

In this episode, we are joined by Dr. Anton Chuvakin, Office of the CISO, at Google Cloud Security where we discuss the evolution of SIEM from...

We are joined this week by John Giglio, director of cloud security for SADA, with tales from the trenches on how automation has helped threat...

Netenrich’s John Bambenek chats with Merys Raymer, Partner Engineering at Google Cloud Security. Merys shares her personal journey as a former threat...

John Pirc, VP and Head of Product Management at Netenrich, explains how customers can improve their threat research using Netenrich's Resolution...

Netenrich's VP and Head of Product Management, John Pirc, discusses how customers can improve their security with data analytics and Resolution...

John Pirc, VP and Head of Product Management, Netenrich, explains how the Resolution Intelligence Cloud works in a Cybersecurity Mesh Architecture...

Netenrich's VP and Head of Product Management, John Pirc, outlines the important business and operational outcomes of using the Resolution...

John Pirc, Netenrich's VP and Head of Product Management, talks about how Resolution Intelligence Cloud works and how it solves the six most critical...
Netenrich's John Pirc, VP and Head of Product Management, highlights the six major security issues addressed by Resolution Intelligence Cloud. He...

Raju Chekuri, Chairman and CEO of Netenrich, says that security is causing a significant shift in the ecosystem. This shift will result in the...

Sharat Ganesh, Head of Product Marketing at Google Chronicle, shares his thoughts on enterprise security concerns. He emphasizes security data for...
















The best source of information for Security, Networks, Cloud, and ITOps best practices. Join us.