3 min read
Configuring Data Ingestion into Google Security Operations: A Step-by-Step Guide
Google Chronicle, part of Google SecOps, is a powerful tool for security data analysis at organizations regardless of size. Using the platform...
Partner Programs
Technology Partners
Key Resources
3 min read
Google Chronicle, part of Google SecOps, is a powerful tool for security data analysis at organizations regardless of size. Using the platform...

6 min read
Threat actors have continued to bypass advanced security tooling despite the...
3 min read
Security leaders today aren’t just defending infrastructure. They are...

5 min read
The rise of sophisticated attack vectors, such as advanced persistent threats...

6 min read
The Chief Information Security Officer (CISO) role has transformed from being...

4 min read
The increasing complexity and scale of cyber threats—fueled by AI and...

5 min read
Security operations (SOC) leaders dream of having a fully scaled unit of...
3 min read
May 21, 2026 by Raju Chekuri
The configuration management database is one of those enterprise systems that...
3 min read
May 19, 2026 by Raju Chekuri
Most security frameworks describe the enterprise as a collection of assets:...
3 min read
May 14, 2026 by Raju Chekuri
Security teams face a persistent vulnerability prioritization problem. At any...
2 min read
Jul 25, 2025 by Michael Beavers
Most security operations centers struggle with scale, complexity, and context....
1 min read
Jul 20, 2023 by Netenrich
Netenrich has entered into a strategic partnership with Cybriant, a leading ...
4 min read
Jul 18, 2023 by John Pirc
To keep an enterprise up and running, security is essential—and no doubt, why...
4 min read
Jun 30, 2025 by Netenrich
Google Chronicle, part of Google SecOps, is a powerful tool for security data...
8 min read
Feb 20, 2025 by Netenrich
The Chief Information Security Officer (CISO) role has transformed from being...
4 min read
Sep 17, 2024 by Raju Chekuri
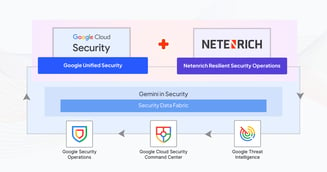
Traditional SIEMs just aren’t cutting it anymore. They rely on outdated,...
9 min read
Nov 12, 2025 by Netenrich
Cyberattacks rarely begin with masterful exploits. They start with small...
8 min read
Nov 11, 2025 by Netenrich
On a regular Monday morning, Maya, an SOC lead, logs into her company’s asset...
7 min read
Nov 11, 2025 by Netenrich
Security Operations Centers (SOCs) are busier than ever. However, are they more...
















The best source of information for Security, Networks, Cloud, and ITOps best practices. Join us.
