Your cloud has no single throat to choke. Neither does your attacker.
Adaptive Cloud Detection & Response correlates posture findings from your CNAPP with real-time runtime signals across your cloud estate; revealing the risks that actually threaten your business.
Speak With an Expert
Unifying Posture, Security Operations, and Risk
Modern cloud attacks rarely appear inside a single tool.
A misconfiguration identified in your CNAPP, a runtime signal fired in your SOC, and an entry in your risk register are often part of the same attack chain; but today they are processed by separate teams, using separate systems, with no shared context.
Adaptive Cloud Detection & Response brings these views together.
Posture findings are enriched with entity context and mapped to existing risks.
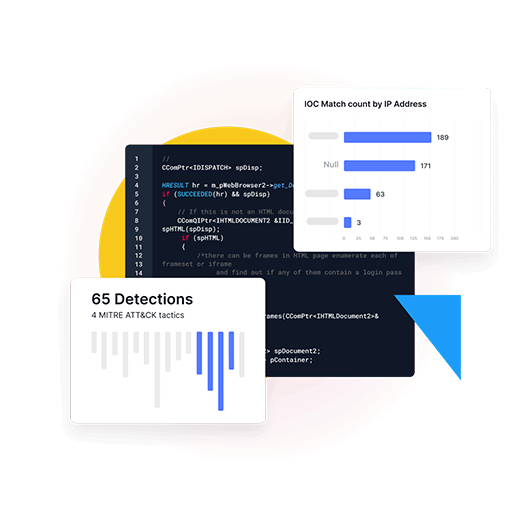
Runtime signals are correlated into situations, scored using Likelihood, Impact, and Confidence (LIC), and resolved into concrete actionable incidents.
When exploitation becomes active, the risk register updates automatically; elevating risks from Potential to Active in real time.

One Solution. Four dimensions. One answer.
Threat
Detect activity across your cloud estate
Runtime detection spans AWS, GCP, Azure, and Kubernetes environments. Signals from cloud control planes, cluster audit logs, identity providers, EDR, data plane events, and pipeline activity are assembled into attack chains, not isolated alerts.
Threat intelligence enrichment and managed response ensure continuous visibility.
Impact
Know what is truly at risk
Entity-aware context that maps every signal to the assets, identities, and data it threatens. Impact converts raw alert volume into business-aligned priority.
- Which IAM role is attached to that instance?
- Is that Lambda function in your payment workflow?
- Does the BigQuery dataset contain regulated data?
- Is the Kubernetes pod running in your production cluster?
Posture
Identify which exposures are actively exploitable
Deep integration with CNAPP platforms (such as Wiz, Prisma Cloud, SCCE, Defender for Cloud, and others) combined with real-time posture-to-signal correlation.
Runtime signals are mapped to the posture condition that made it possible. Every posture finding is validated against detection coverage so remediation focuses on what attackers can actually reach.
Risk
Answer the question security leaders care about every Monday morning
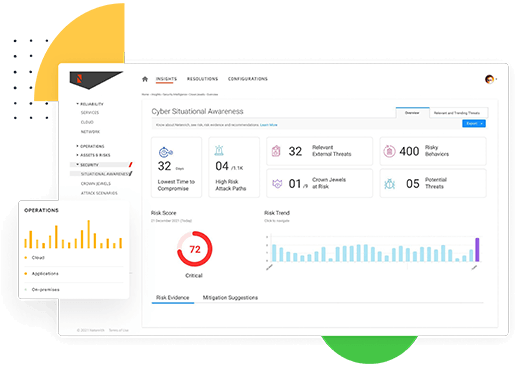
A dynamic risk register continuously scoring exposures using Likelihood · Impact · Confidence.
Risks move automatically from Potential to Active Exploitation as signals arrive, producing Actionable recommendations your SOC can execute immediately.
Not thousands of findings sorted by CVSS. Just a handful of risks that actually threaten the business.
Solution Capabilities
Adaptive CDR
Continuous detection and response across identity, control plane, network activity, workloads, and data stores across AWS, GCP, Azure, and Kubernetes.
-
Continuous Ingestion Ingests AWS CloudTrail, VPC Flow Logs, GCP audit logs, Azure activity logs, EKS/GKE/AKS audit trails, and serverless execution telemetry all normalized into a unified signal layer.
-
Behavioral Detection Detects credential abuse, account takeover, API misuse, lateral movement, container escapes, and data exfiltration patterns across clouds identities and infrastructure.
-
MITRE ATT&CK Mapping Maps detections to cloud-relevant TTPs so analysts see real attacker behavior rather than isolated alerts.
Adaptive CDR + Posture
Correlates configuration findings with live runtime signals, ensuring remediation focuses on what is actively exploitable.
-
Evidence-Driven Prioritization Every runtime signal is mapped to the posture condition that enabled it. Every posture finding is checked for detection coverage.The result: remediation decisions driven by active exploitation, not CVSS scores.
-
Posture Roadmap Focuses remediation on the handful of posture conditions and weaknesses that materially reduce real risk.
-
Dynamic Risk Register Findings move from Potential to Active Exploitation in real time as signals arrive. The register reflects the current threat state, not last week's scan.
Built on Netenrich Resolution Intelligence Cloud™
The Resolution Intelligence Cloud™ is the engine behind Adaptive Cloud Detection & Response. It unifies security data across posture, runtime, and identity, applies AI-driven analytics, and orchestrates autonomous response across your cloud environment.
Evidence-Backed Verdicts
Signals are scored using the LIC model (Likelihood · Impact · Confidence) to produce high-confidence incidents with clear business context.
Situation Formation
Signals across clouds, tools, and timelines are correlated into a complete attack narrative; with blast-radius analysis and decision-ready context.
Vendor-Agnostic Ingestion
Findings from Wiz, Prisma Cloud, SCCE, Orca, Defender for Cloud, and other platforms are correlated alongside runtime telemetry.

What Netenrich detects that your current stack misses
Each of these represents a class of attack that produces no single high-confidence alert in isolation, but becomes obvious when posture, runtime signals, and business context are correlated.
EC2 compromise via IMDS credential abuse
Kubernetes container breakout → IAM role pivot → S3 data access
CI/CD pipeline abuse via leaked credentials
SaaS OAuth compromise → GCP pivot via service account key
Dormant IAM credential reactivation leading to privilege escalation
Serverless Lambda chain attack leveraging public function URLs
Firestore low-and-slow PII extraction over extended time periods say: 5 docs every 30 seconds for 48 hours, never crossing a spike threshold, rebuilding the entire database offline.
BigQuery Vertex AI agent exfiltration: An AI service account summarizing sensitive tables into an external prompt. Legitimate API calls. Zero OOTB detection.
BigQuery VPC-SC bypass via authorized view: Jobservice.insert creates an authorized view in an external project, bypassing VPC Service Controls entirely.
Azure Managed Identity token reuse: UAMI token harvested from IMDS, exfiltrated, reused from external IP hours later. Three Defender events, zero Sentinel correlation.
Azure DevOps → ARM template injection → subscription takeover: YAML pushed to unprotected branch deploys ARM template that creates Owner-level service principal.
GitHub to cloud attack chain: hardcoded key in repo, exfiltrated via CI logs, used to assume production IAM role 47 days later.
Dormant IAM credential reactivation: decommissioned vendor key re-enabled via UpdateAccessKey API. No SIEM watches for reactivation. Only for creation and deletion.
SaaS OAuth to GCP cloud pivot: overprivileged OAuth app exposes Workspace admin API, stale SA key extracted, GCP Cloud Storage accessed with no endpoint signal.
How Adaptive Cloud Detection & Response Closes the Gaps
Modern cloud attacks traverse domains before they appear as threats. An EC2 compromise becomes credential theft. Credential theft becomes S3 exfiltration. A Kubernetes misconfiguration becomes an IAM pivot. A repository secret becomes a production account takeover weeks later.
What makes these attacks possible is not just runtime behavior, it is the posture conditions that already exist. And what makes them difficult to detect is that no single tool sees the entire chain. Adaptive Cloud Detection & Response correlates across clouds, services, and identities; assembling the kill chain that individual tools only glimpse in fragments. The result is a small set of reachable, active, and actionable risks.
Outcome Delivery Model
Onboarding & Enablement
Log integration, entity mapping, CNAPP connection, and baseline activation of the detection and correlation engine.
Continuous Protection
24×7 monitoring, situation formation, risk register updates, and actionable incidents guidance for identity, workloads, and data across your cloud estate.
Improvement & Maturity
Monthly detection effectiveness reviews, posture-to-signal gap reporting, architectural recommendations, and executive risk reporting.
Ready for High-Confidence Security?
Get SOC-ready narratives, full attack timelines, and actionable incidents powered by Netenrich.
Work from a common operational view
Siloed security and digital ops leads to gaps and inefficient duplication of tools, processes, and people. Resolution Intelligence Cloud provides a common operational view and situational awareness aligned to business risk. And it facilitates collaboration within and between teams.
- Strengthen your security posture
- Improve performance and up time
- Boost analyst effectiveness
Out-innovate hackers with anomaly detection & situational awareness
Hackers are relentlessly innovative. It's futile to fight them with traditional, reactive methods.
- Identify unknowns without detection rules with advanced anomaly detection (think next-next-gen UEBA)
- Be proactive with actionable insights from data over time, correlated and mapped to the MITRE ATT&CK framework
- Identify and resolve what matters most to the business — stop wasting time on alert noise
- Communicate across functions and coordinate response fast